Two-factor authentication is one of the easiest ways for people to protect any online account. So, of course criminals are trying to circumvent that protection.
Intel 471 has seen an uptick in services on the cybercrime underground that allow attackers to intercept one-time password (OTP) tokens. Over the past few months, we’ve seen actors provide access to services that call victims, appear as a legitimate call from a specific bank and deceive victims into typing an OTP or other verification code into a mobile phone in order to capture and deliver the codes to the operator. Some services also target other popular social media platforms or financial services, providing email phishing and SIM swapping capabilities.
All the services Intel 471 has observed, which have only been in operation since June, either operate via a Telegram bot or provide support for customers via a Telegram channel. In these support channels, users often share their success while using the bot, often walking away with thousands of dollars from victim accounts.

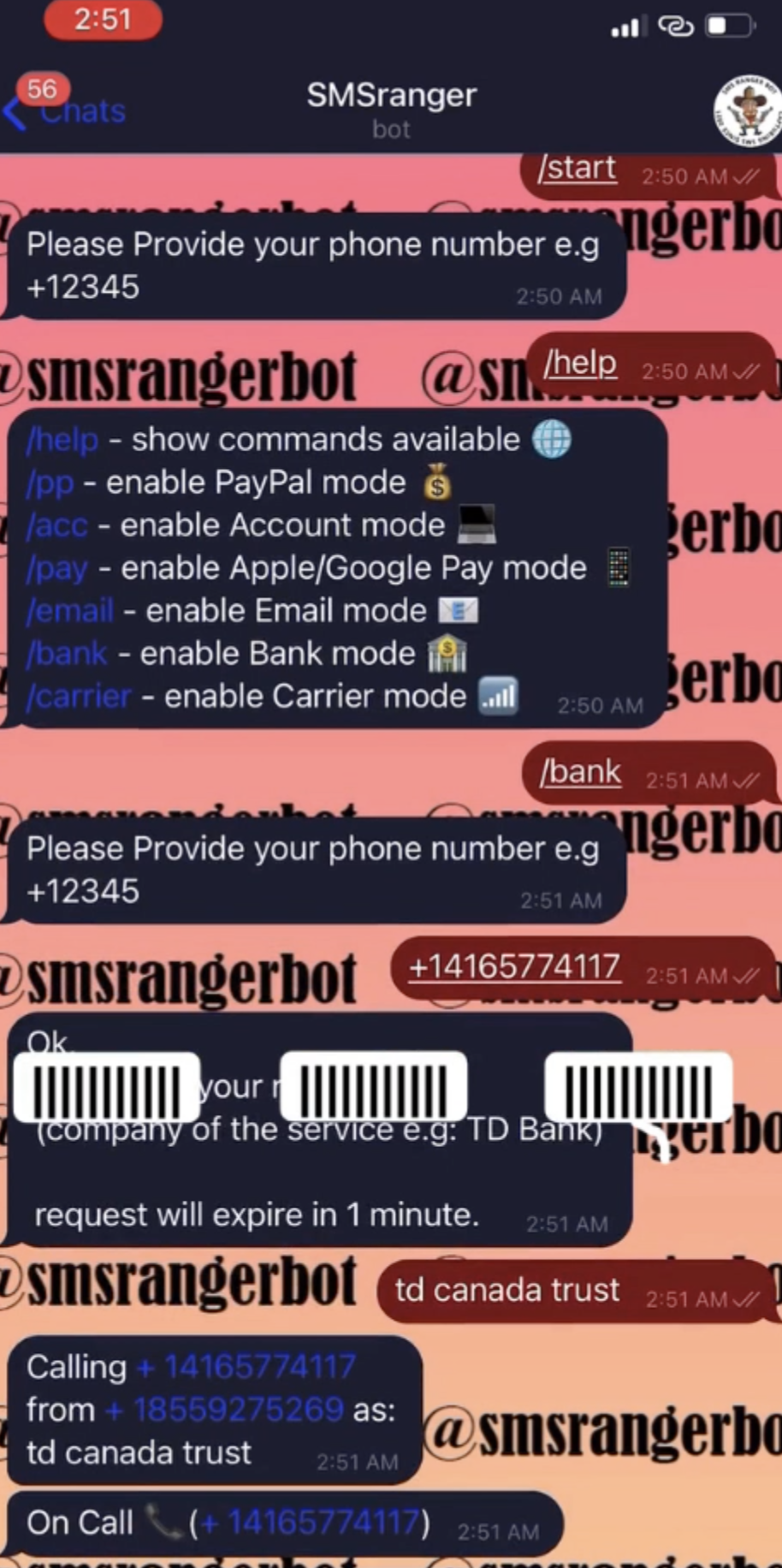
One particular bot, known as SMSRanger, is extremely easy to use. Those who pay for access can use the bot by entering commands similar to how bots are used on popular workforce collaboration tool Slack. A simple slash command allows a user to enable various “modes” — scripts aimed as various services — that can target specific banks, as well as PayPal, Apple Pay, Google Pay, or a wireless carrier. Once a target’s phone number has been entered, the bot does the rest of the work, ultimately granting access to whatever account has been targeted. Users claim that SMSRanger has an efficacy rate of about 80% if the victim answered the call and the full information (fullz) the user provided was accurate and updated.
Another bot, known as BloodOTPbot, also worked in the ability to send users a fraudulent OTP code via SMS. The bot requires an attacker to spoof the victim’s phone number and impersonate a bank or company representative. The bot then would attempt to call the victim and use social engineering techniques to obtain a verification code. The operator would receive a notification from the bot during the call specifying when to request the OTP during the authentication process. The bot would text the code to the operator once the victim received the OTP and entered it on the phone’s keyboard.
A user needed to pay a monthly fee of US $300 to obtain the authentication code required to operate the bot. Additionally, users could pay anywhere from US $20 to $100 more for live phishing panels that target accounts on social media networks like Facebook, Instagram, and Snapchat, financial services like PayPal and Venmo, investment app Robinhood, and cryptocurrency marketplace Coinbase.
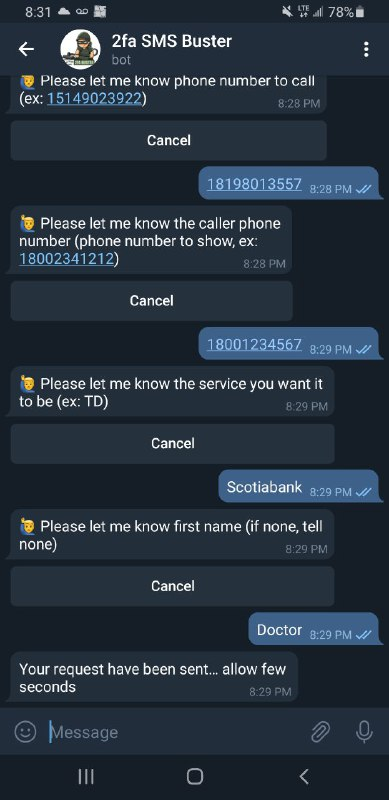
Yet another bot, known as SMS Buster, requires a bit more effort from an actor in order to obtain account information. The bot provides options to disguise a call to make it appear as a legitimate contact from a specific bank while letting the attackers choose to dial from any phone number. From there, an attacker could follow a script to track a victim into providing sensitive details such as an ATM personal identification number (PIN), card verification value (CVV) and OTP, which could then be sent to an individual’s Telegram account. The bot, which was used by attackers targeting Canadian victims, gives users the chance to launch attacks in French and English.
As of this blog post’s publication date, Intel 471 has seen accounts illegally accessed at eight different Canadian-based banks.
The ease by which attackers can use these bots can not be understated. While there’s some programming ability needed to create the bots, a bot user only needs to spend money to access the bot, obtain a phone number for a target, and then click a few buttons. A video demo for one of these bots shows how easy it is to launch an attack.
Overall, the bots show that some forms of two-factor authentication can have their own security risks. While SMS- and phone-call-based OTP services are better than nothing, criminals have found ways to socially engineer their way around the safeguards. More robust forms of 2FA — including Time-Based One Time Password (TOTP) codes from authentication apps, push-notification-based codes, or a FIDO security key — provide a greater degree of security than SMS or phone-call-based options.
Ten articles before and after
The public sector is a juicy target for cybercriminals
Cybercriminals cash in on black market vaccine schemes
Cybercrime underground flush with shipping companies’…
How cryptomixers allow cybercriminals to clean their…
Emotet is back. Here's what we know.
Manufacturers should focus on protecting their supply…
How Groove Gang is shaking up the…
How BEC scammers use the cybercrime underground